
BANANA

|
a Tool
for Boundary Ambients Nesting ANAlysis
|
| |
|
| |
|
|
A screen-shot of the BANANA tool is shown in the following figure.
The following figure gives an overview of the
architecture of the tool 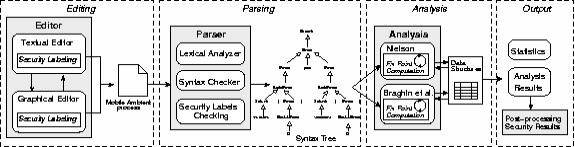
The user can then choose to launch either the Nielson
or the Braghin et al. analysis. Once the analysis has started the tool parses
the process, builds a syntax tree and computes the fix point algorithm yielding
an over-approximation of all possible ambient nestings. |